Event JSON
{
"id": "cb797276aed4d669b4aa243ced222f3f00a85418b94b92e9b68c2f03e38a4ccd",
"pubkey": "d6149823c90c4865e4bc434a4be1a1ee8f72aabd8328dd059ba4f11f7633b0b6",
"created_at": 1708206219,
"kind": 1,
"tags": [
[
"t",
"unbound"
],
[
"t",
"unbound"
],
[
"t",
"DNS"
],
[
"t",
"dns"
],
[
"t",
"networking"
],
[
"t",
"networking"
],
[
"t",
"linux"
],
[
"t",
"linux"
],
[
"r",
"https://image.nostr.build/761e9301bb1cc6a6de124ed56b7168e3f6b2a4e045a7322eb656f4b9f497aabb.jpg"
],
[
"r",
"https://image.nostr.build/bbda8a53deef3cb55d59c0ad7464d3dc0b289d7a963b7bc6da7c1ef60c1af7c5.jpg"
],
[
"imeta",
"url https://image.nostr.build/761e9301bb1cc6a6de124ed56b7168e3f6b2a4e045a7322eb656f4b9f497aabb.jpg",
"m image/jpeg",
"alt Verifiable file url",
"x cbc6fa5eb901cf6732d3041fd61b7af243105bd7e19ee4be24665c7da2d402de",
"size 53168",
"dim 1253x324",
"blurhash H37Kxb~qS6tQxutQbIRjR,IVt6xuRQV@jcoLofoe",
"ox 761e9301bb1cc6a6de124ed56b7168e3f6b2a4e045a7322eb656f4b9f497aabb"
],
[
"imeta",
"url https://image.nostr.build/bbda8a53deef3cb55d59c0ad7464d3dc0b289d7a963b7bc6da7c1ef60c1af7c5.jpg",
"m image/jpeg",
"alt Verifiable file url",
"x be264dea6ca5e9b80e49c0c63d53fd6ea94a0c12c40a44105be2ed956a9a16cc",
"size 50117",
"dim 1253x272",
"blurhash H47nau_NE1W-x]tQR*R%WrogxtjrMxRjfSWBoft7",
"ox bbda8a53deef3cb55d59c0ad7464d3dc0b289d7a963b7bc6da7c1ef60c1af7c5"
]
],
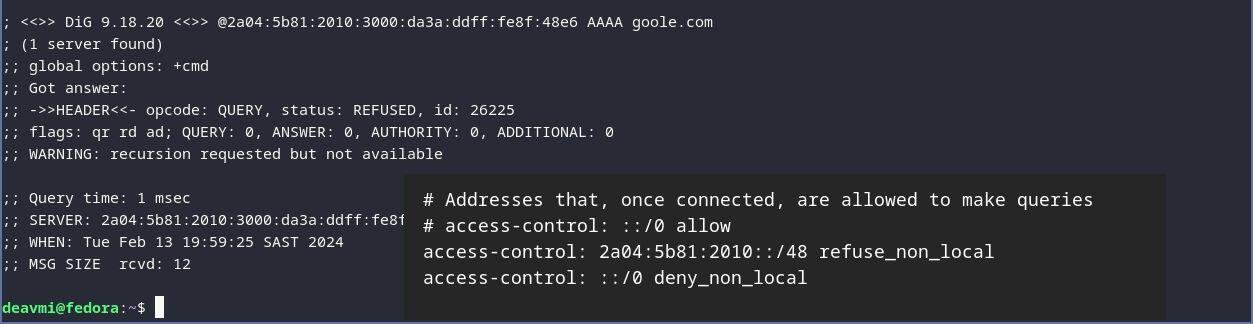
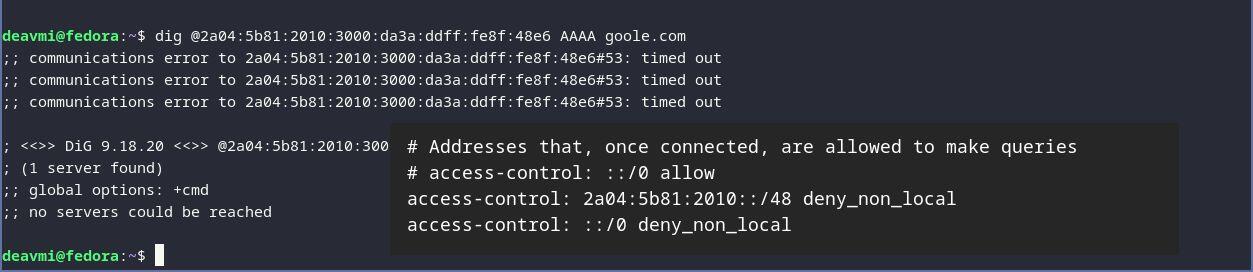
"content": "Been playing around with configuring my future authoritative name server and recursive resolver using Unbound!\n\nI've always found the discrepency, in network services, to report failures but also remain stable against forms of abuse. By this I mean, should you report when a subnet or host is unreachable via a an \"ICMP Destination Network Prohibited\" or not - what if you receive so much traffic that you end go transmitting a load of errors. Never mind amplification attacks that can be done with connectionless protocols like (in this case ICMP).\n\nA same sort of possibility is there for DNS (when using UDP at least). Below are the two options to refuse anyone in my allocated subnet access to the resolver (only authoritative zone data can be queried).\n\nOne wants to remain secure against attacks but at the same time, useful network reporting is helpful.\n\n#unbound #DNS #networking #linux\n\n\nhttps://image.nostr.build/761e9301bb1cc6a6de124ed56b7168e3f6b2a4e045a7322eb656f4b9f497aabb.jpg\n\nhttps://image.nostr.build/bbda8a53deef3cb55d59c0ad7464d3dc0b289d7a963b7bc6da7c1ef60c1af7c5.jpg",
"sig": "56b22703f8bd36267a5c36f11bc4220cf4928ccdb7fcd2ad3087095e2a87402260b9442eace24e8cab399a9576c93427fe129ee34de43bb5a9a584dd82ff5996"
}